Meeting Regulatory Standards for API Data Protection
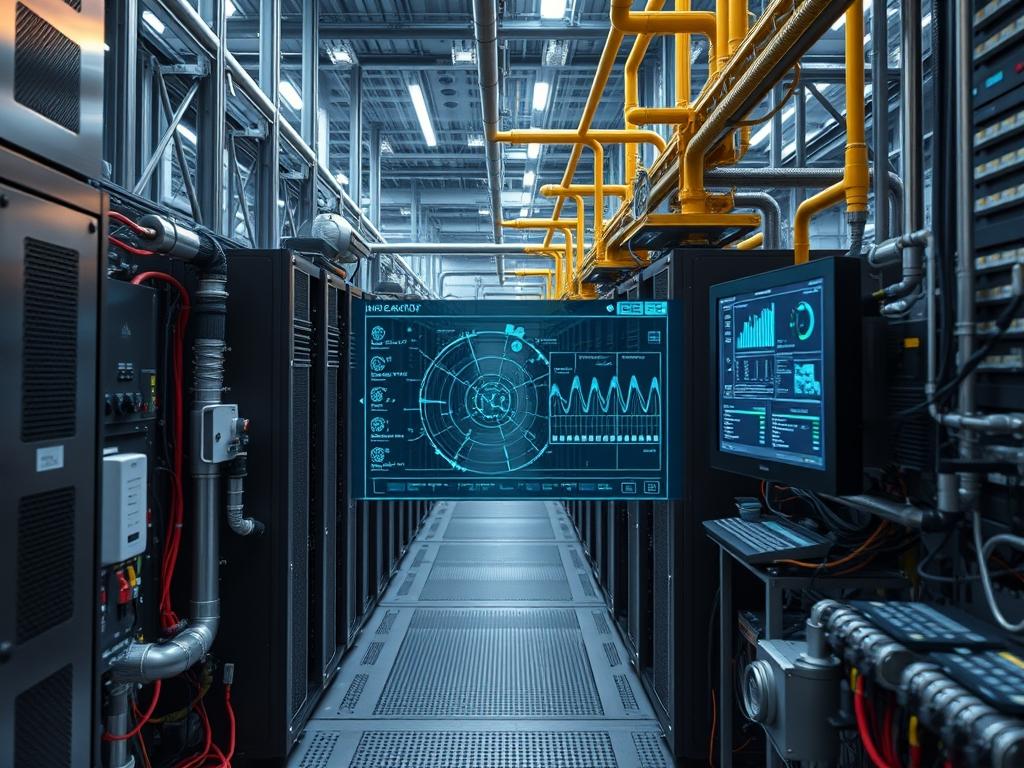
API Security Compliance serves as the primary governing framework for sanitizing and protecting sensitive data as it traverses networked interfaces. Within a distributed infrastructure, the API layer acts as the enforcement point between untrusted clients and the internal data plane. This system bridges application logic and network transport, requiring strict adherence to protocols like TLS … Read more